How to recognize and avoid phishing attacks
Cybercriminals engage in fraudulent activity on the internet. A lot of businesses recognize this as a challenge, and as a result, they run campaigns where they give advice against giving out some information that they will never ask customers for. Their aim in doing this is to make customers aware that they need to take responsibility for some aspects of their security and protect themselves from these cybercriminals.
These cybercriminals are trying to gain access to your information and steal your money or other confidential data. There’s a popular term for what they do, and it’s called Phishing.
What is Phishing?
Phishing is the fraudulent attempt to obtain sensitive data (such as passwords, ATM card pins, or other sensitive details) by digitally impersonating a trustworthy entity.
Have you ever gotten an email from someone claiming to be a bank? Have you ever gotten a text message from a fake brand asking you to click a link for a discount?
If your answer is was yes to one or both of those questions, you have been phished.
How to identify phishing attacks
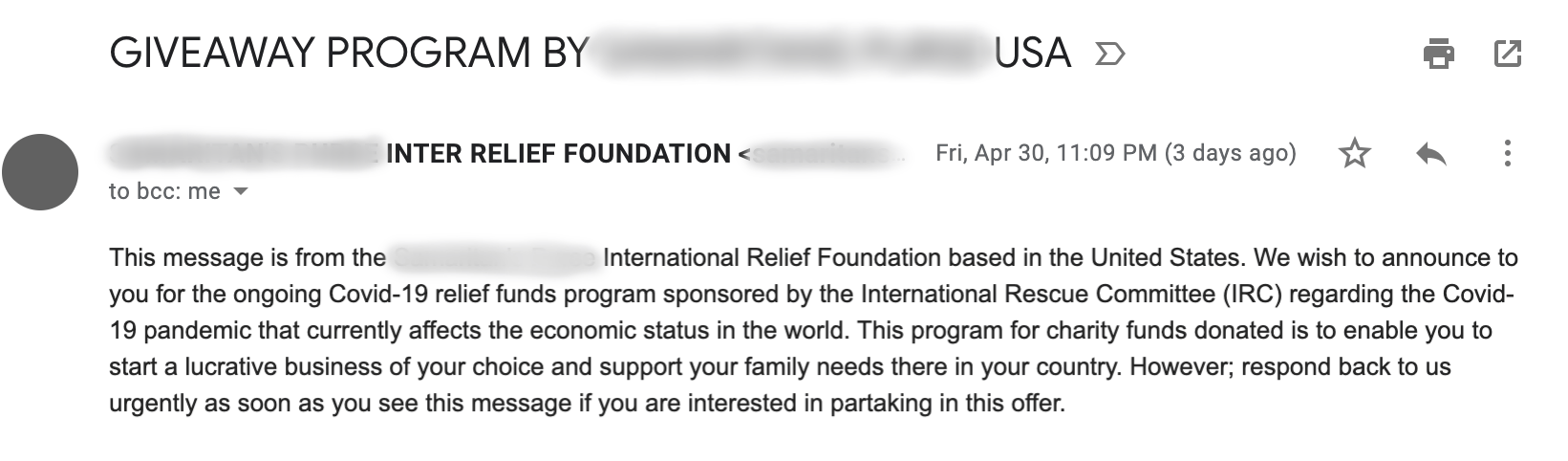
Phishing occurs in multiple ways. A lot of phishing scenarios I have come across involved cybercriminals sending emails (like the image above) or text messages.
However, phishing occurs beyond these channels as well. Cybercriminals can create fake websites, distribute malware all over the internet (and have people install them), create fake public “WiFi” for people to connect to, leave phone calls, or leave voice messages. They can even use ads to make you click their links.
There are many common real-life phishing examples. A few are:
- “Your account has been hacked/deactivated”
- “Your ATM card has been compromised”
- “Social media friend request”
- “Your subscription expires soon”
How to avoid phishing scams
-
Always validate the source of any communication you receive before acting on it.
-
Avoid opening attachments contained in suspicious emails.
-
Educate people in your organization about phishing scams so that they can protect themselves.
-
Avoid entering personal information in unknown forms on the internet.
-
Always use secure software.
-
Enable multi-factor authentication.
-
Install phishing filters on your browser and email apps.
Unlock your potential: Phishing series, all in one place!
To continue your exploration of phishing attacks, check out our series of Answers below:
What is phishing?
Learn about phishing, a deceptive tactic used to steal sensitive information.How to recognize and avoid phishing attacks
Discover how to identify phishing attempts and protect yourself from online fraud.What is the difference between phishing and spoofing?
Understand the key differences between phishing and spoofing to improve your defenses.What is the difference between hacking and phishing?
Explore how phishing differs from hacking in the world of cybersecurity.