What is Event Injection?
Several web applications provide extra layers for protection. These layers prevent unnecessary exposure that may be caused by common programming or coding mistakes. It is very important to make sure that applications do not become vulnerable.
What are Event Injection Attacks?
Serverless functions are easily connected to the cloud. This makes many device functions vulnerable and provides a false sense of security. Coding becomes less defensive by constant reliance on cloud providers, which compromises overall security. Serverless programs are referred to as “event-driven” – this means that many applications can be activated by various sources and encodings. It also circumvents the security provided by many protection layers; thus, making them vulnerable to attacks.
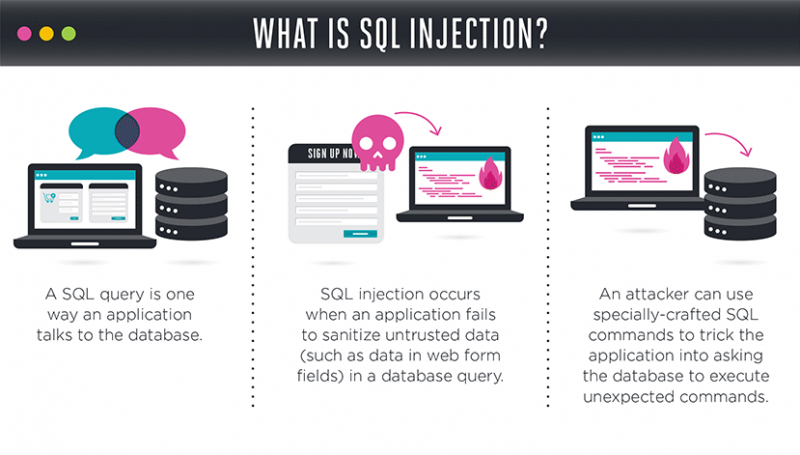
Events services, such as cloud storage, email, notifications, etc., usually trigger serverless architectures. Any serverless function that is defenseless against any form of injection attack is referred to as an event injection. Examples include SQL Injection, OS Command Injection, Code Injection, and many more that are consistently used by hackers to exploit functions and defense mechanisms.
Prevention
Free Resources