Social Defense
Explore how to develop a vigilant organizational culture to combat phishing attacks. Learn to train colleagues to recognize phishing signs like urgent emails, suspicious domains, and unsafe attachments. Understand the importance of supportive reporting and practical verification methods to minimize damage from phishing.
We'll cover the following...
You’ll want to provide training for the people in your organization so they develop a healthy level of skepticism toward incoming email. You can put the training together yourself or hire an outside firm. Your best defense is vigilant colleagues. Most phishing attacks spread a wide net, so increasing the likelihood that even one person notices the deception allows you to respond and get the word out sooner. We’ll cover phishing responses later in this chapter.
Here are the basic points you’ll want to emphasize in your anti-phishing training.
- Don’t embarrass your colleagues.
- Be extra skeptical about emails with urgent deadlines.
- Be suspicious of strange-looking domains in links and email addresses.
- Be skeptical about attachments.
- Consider whether the premise of the email makes sense.
Let’s look at each of these points.
First, you need to make sure that if people get phished they’ll feel safe enough to report that right away. People won’t feel safe if they’re teased or blamed for getting phished. They won’t feel safe if they see those things happen to someone else, either. The sooner you find out that someone handed over their credentials, the less damage there will be. If your colleagues are worried that they’ll get in trouble for coming forward and announcing that they got phished, they are more likely to just clam up and hope the whole thing blows over without telling anyone.
A trait common to many phishing emails is a sense of urgency to get the victim to act quickly. One example of this is a phishing email that was forged to appear to be sent by a company executive who needs help handling an important customer request right away. Another example is a phishing email that pretends to be from a vendor who hasn’t been paid for an invoice and needs payment right away. These are just pretenses to get the recipient to act quickly without thinking through what they’re doing or what websites they’re entering their password into.
Another trait that is common to phishing emails is that they are often forged to look like they were sent from someone legitimate. Email uses several headers related to the identity of the sender, including From and Reply To. Be suspicious when these headers don’t all match. Also, be aware when the domains in use in these fields are not familiar. Phishers will sometimes register new domains that look like legitimate domains and send emails from these domains. Examples of this would be registering a domain like fo0.com (the second letter o is replaced with a zero) and sending an email from ceo@fo0.com when trying to phish people at foo.com. These doppelgänger domains can also be used in links in the email. So remind colleagues to be suspicious of doppelgänger domains in the email headers and in links within the email.
Remind your colleagues to be suspicious of the links in an email. If an email claims to link to a shared document on outlook365.com, but the actual link points to sites like outl00k365.com, outlook356.somefilesharingservice.com, outlooook365.com, or ou.tlook365.com, be careful. This type of domain name is often a sign that the email is fraudulent.
Encourage your colleagues to go with their gut when reading emails. Does the email “feel” right? Set aside all the technology. Does the premise of the email make sense? If an email is asking you to take urgent action to address an unpaid vendor but your role in your company doesn’t have you interacting with vendors, then slow down and think about whether this email is legitimate. If the email claims to be from an important executive who needs your help right away but that executive has never asked you for this kind of help, seek independent verification of the email.
It is important to be skeptical about attachments. Don’t open any attachment unless you were already expecting an attachment from the sender. If you must open an attachment, be sure that the file extension of the attached file is appropriate for the kind of attachment you’re expecting. For instance, if you’re expecting to receive a jpg image from someone, be sure that the file name ends in “.jpg” or “.jpeg”, not “.jpg.exe”. A file with a name ending in “.exe” is generally a program, not a picture. So if you download an “.exe” file and double-click on it, the phisher’s program will run on your computer. Finally, if you must open Microsoft Office documents from an email, be sure to disable macros in Microsoft Office before opening the document.
If there is any question about the legitimacy of an email, verify the claims of the email without using the links in the email. In particular, don’t trust links that ask you to log in to something. If the email claims to link to a shared document but the link presents you with a login screen, don’t log in using that link. Instead, log into the file-sharing service as you normally would, then use the search capabilities of that file-sharing service to find the files that allegedly require your attention. If the email is legitimate, you’ll find them. Similarly, if the email claims to be from someone at your company but something just feels off about it, walk over to their desk and ask if they really sent it.
Whatever training you decide on, be sure to make that training part of your onboarding process for new employees. Training isn’t a one-time event; it has to keep up with the growth of your organization. Also be sure to offer refresher courses to staff who’ve been with the organization for a while. This will help keep everyone vigilant and keep everyone up-to-date on recent changes in the phishing landscape.
You’ll want to run test phishing campaigns against your organization to help illustrate the importance of not clicking on links. One tool that can be useful in this is Gophish, an open-source phishing campaign tool. It’s important to do this in a way that won’t erode the relationship with the rest of the company. You’ll want to announce that periodic phishing campaigns are part of the security posture of your organization. You’ll want to have some kind of refresher training or readings for people who fall for the phishing email, but it’s important to not single them out or embarrass them. Expect people to have questions and be glad for their interest.
It’s good to develop the capabilities to investigate phishing emails. Keeping up with incoming phishing emails can quickly turn into a full-time job, though. So you’ll probably only be able to investigate a small percentage of them. Even if you don’t have the capacity to investigate them all, it’s still worthwhile to train your organization to forward them all to a queue for investigation. First, this reinforces the anti-phishing training you’ll want to give to your organization. Second, this will serve as a good record of what attacks have been attempted if you do have an incident.
Don’t DIY
Before we get into DNS-based defenses, here’s a simple piece of advice about email hosting—don’t do it yourself. Just host your company’s email with G Suite from Google. (Ok, you could also pick Outlook 365 if you like Microsoft. There are other email hosting options, but I don’t believe any of them are able to put as many resources into security as these two companies do.) It’s a lot of work just to keep a mail server up and running with the reliability that email requires. It’s even more work to keep it patched and configured securely. Maintaining a mail server is a full-time job. And if you want support on holidays, weekends, evenings, and sick days, it’s a full-time job for more than one person.
If your organization is just starting out, you have much better ways to use your employees’ time than maintaining a mail server. Even if you’ve grown to 200 employees and use Google’s most expensive hosting plan, you’d still spend less on G Suite than the cost of a single US-based full-time engineer. All three of the DNS tools we’ll cover work with G Suite but aren’t enabled out of the box. It’s pretty straightforward to enable them as long as you have permissions to edit DNS records for your domain. G Suite maintains good documentation on all three of these tools.
Q U I Z
Is the following a phishing email?
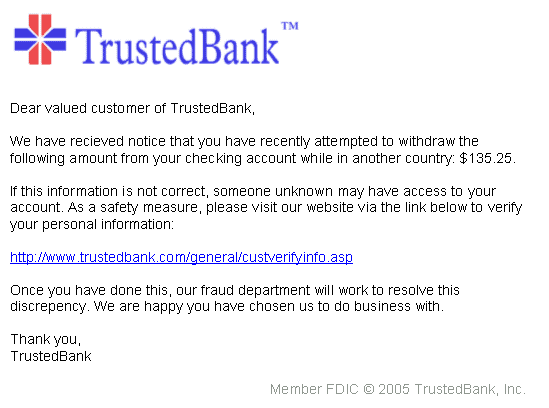
Yes
No
In the next lesson, we’ll study some DNS-Based defense.