AI-powered learning
Save this course
Become a Blockchain Developer
Gain insights into blockchain technology, delve into cryptography, explore Hyperledger Fabric, and learn to deploy networks, chaincode, and manage user identities through hands-on development.
4.4
31 Lessons
6h
Updated this week
Join 3 million developers at
Join 3 million developers at
LEARNING OBJECTIVES
- Identify key blockchain features (immutability, distribution) and explain how they address trust issues
- Use hash functions (e.g., SHA256) to verify data integrity and explain their role in block linking
- Apply public key cryptography, digital signatures, and PKI to secure communication and verify identities
- Analyze blockchain data structures and consensus at a high level, including basic Bitcoin transaction concepts
- Deploy a Hyperledger Fabric network with Docker, generating crypto material, genesis block, and channels
- Write and deploy JavaScript chaincode to perform CRUD operations and test invocations via CLI
- Build a Node SDK client app using gateways and wallets to enroll users, query ledgers, and invoke chaincode
Learning Roadmap
1.
Introduction - Understanding Blockchain
Introduction - Understanding Blockchain
Get familiar with blockchain fundamentals, addressing trust issues in various industries.
2.
The technology pre-reqs for understanding blockchain
The technology pre-reqs for understanding blockchain
Grasp the fundamentals of cryptography, hash functions, public key cryptography, digital signatures, and PKI for blockchain.
3.
Blockchain data storage
Blockchain data storage
3 Lessons
3 Lessons
Examine blockchain's decentralized data storage, interactive playground experimentation, and its distributed network structure.
4.
Understanding the value of blockchain (Bitcoin example)
Understanding the value of blockchain (Bitcoin example)
3 Lessons
3 Lessons
Grasp the fundamentals of Bitcoin's history, mining process, and factors driving its value.
5.
Hyperledger Fabric - Concepts
Hyperledger Fabric - Concepts
4 Lessons
4 Lessons
Take a closer look at Hyperledger Fabric's core concepts, including network structure, transaction processing, and development components.
6.
STEP 1: Deploy first Fabric Network
STEP 1: Deploy first Fabric Network
2 Lessons
2 Lessons
Tackle deploying a Hyperledger Fabric network using Docker, including setup, initialization, and configuration.
7.
STEP 2: Write and deploy Chaincode
STEP 2: Write and deploy Chaincode
2 Lessons
2 Lessons
Master the steps to write and deploy chaincode for secure blockchain interactions.
8.
STEP 3: Create a Client Application
STEP 3: Create a Client Application
4 Lessons
4 Lessons
Step through creating a client application, integrating wallets, identities, and deploying on blockchain.
Certificate of Completion
Showcase your accomplishment by sharing your certificate of completion.
Complete more lessons to unlock your certificate
Developed by MAANG Engineers
ABOUT THIS COURSE
In this course, we will build blockchain concepts from the ground up. We will start with basic cryptography constructs, like hash functions and PKI encryption, to first build a solid base for understanding blockchain and appreciate its value. Then, we will explore the Hyperledger Fabric technology by IBM using hands-on development environment within your browser. This course is a great starting point for engineers looking to develop expertise in blockchain technology with Hyperledger Fabric specialty. In this course, you will deploy your own blockchain network, deploy chaincode on it and create an application that invokes your chaincode running in fabric network. You will also learn to manage fabric user identities in your application using wallets.
ABOUT THE AUTHOR
Huma Q
Seasoned Software Architect. Engineering Leader.
Trusted by 3 million developers working at companies
A
Anthony Walker
@_webarchitect_
E
Evan Dunbar
ML Engineer
S
Software Developer
Carlos Matias La Borde
S
Souvik Kundu
Front-end Developer
V
Vinay Krishnaiah
Software Developer
Built for 10x Developers
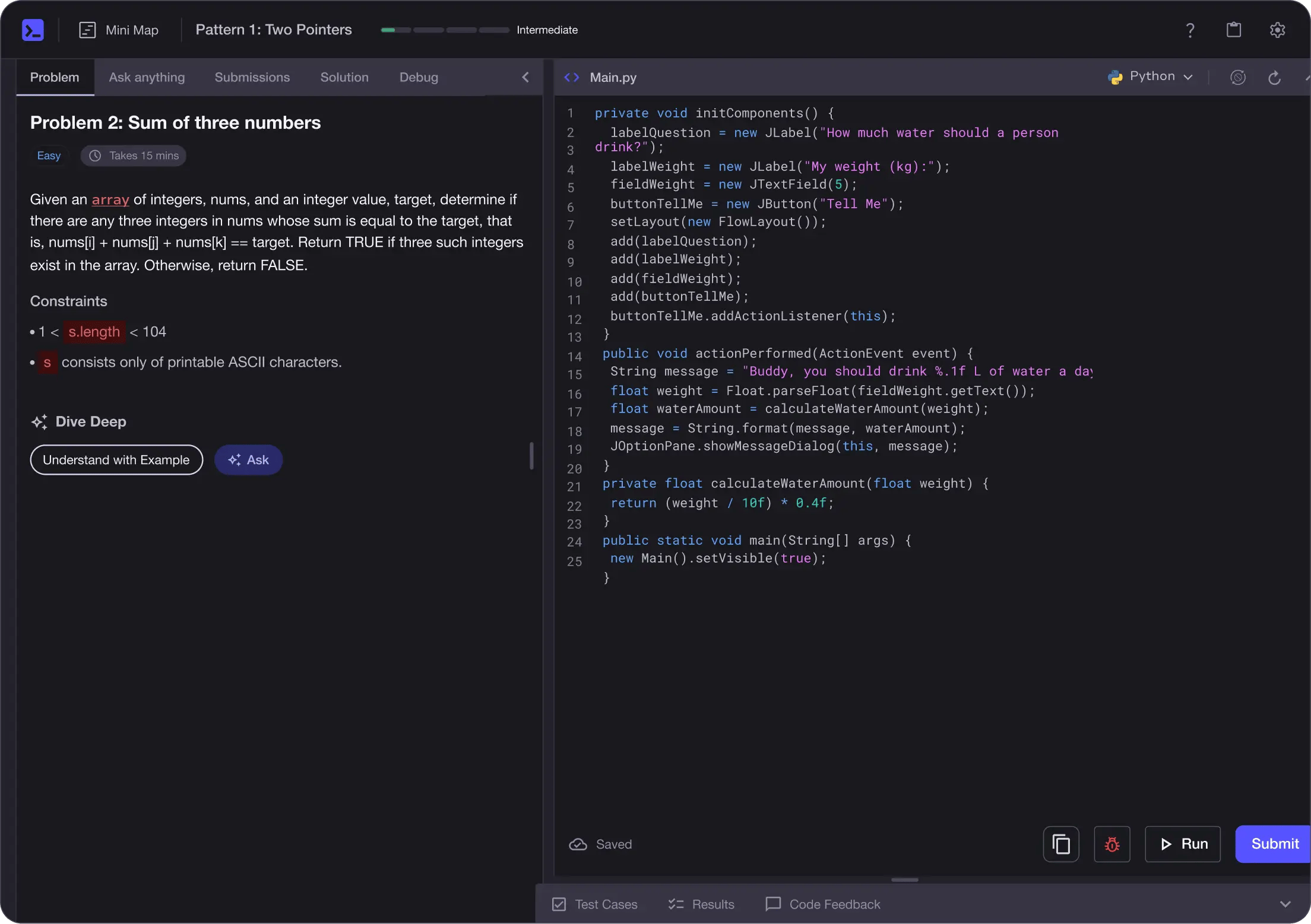
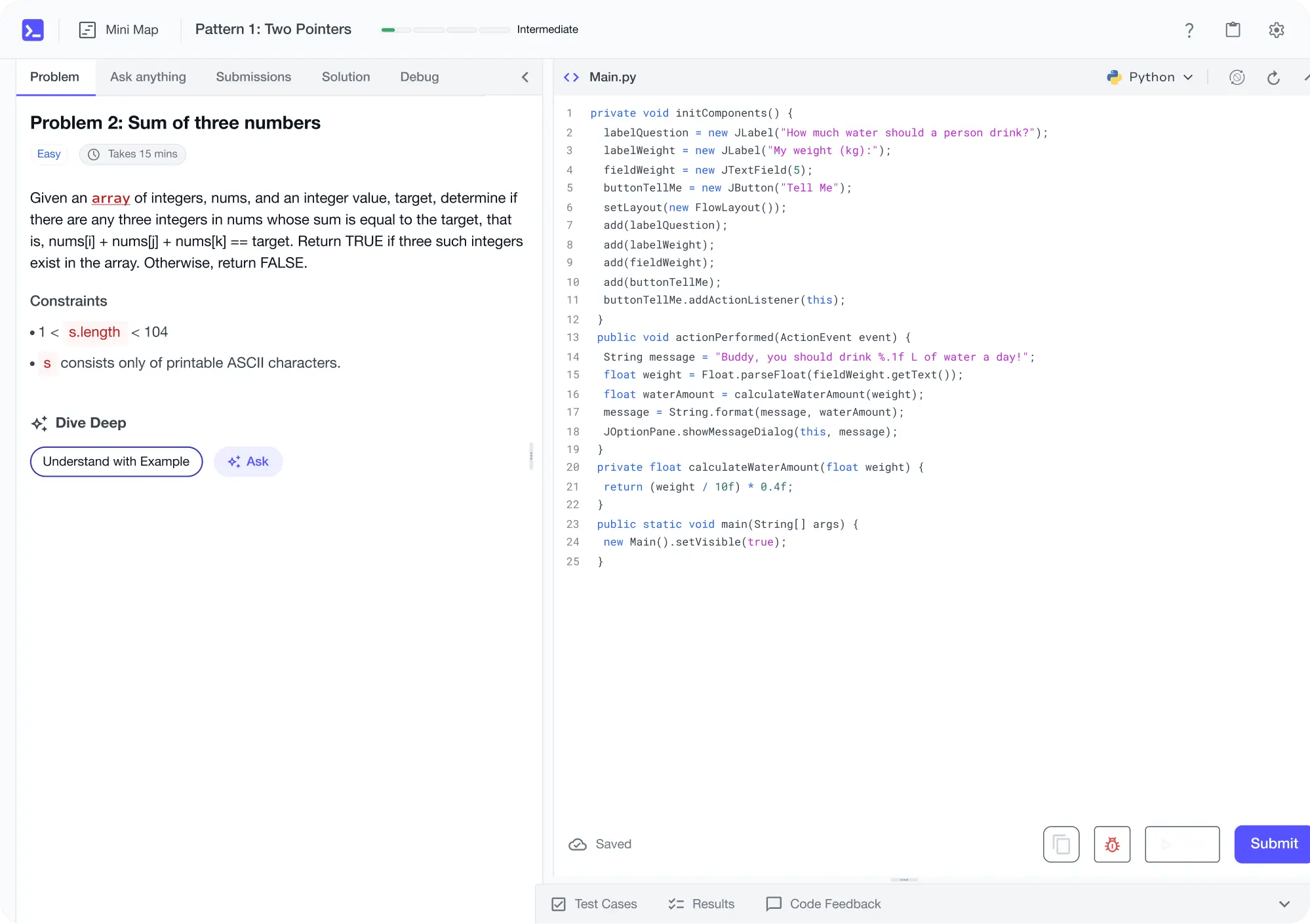
No Passive Learning
Learn by building with project-based lessons and in-browser code editor
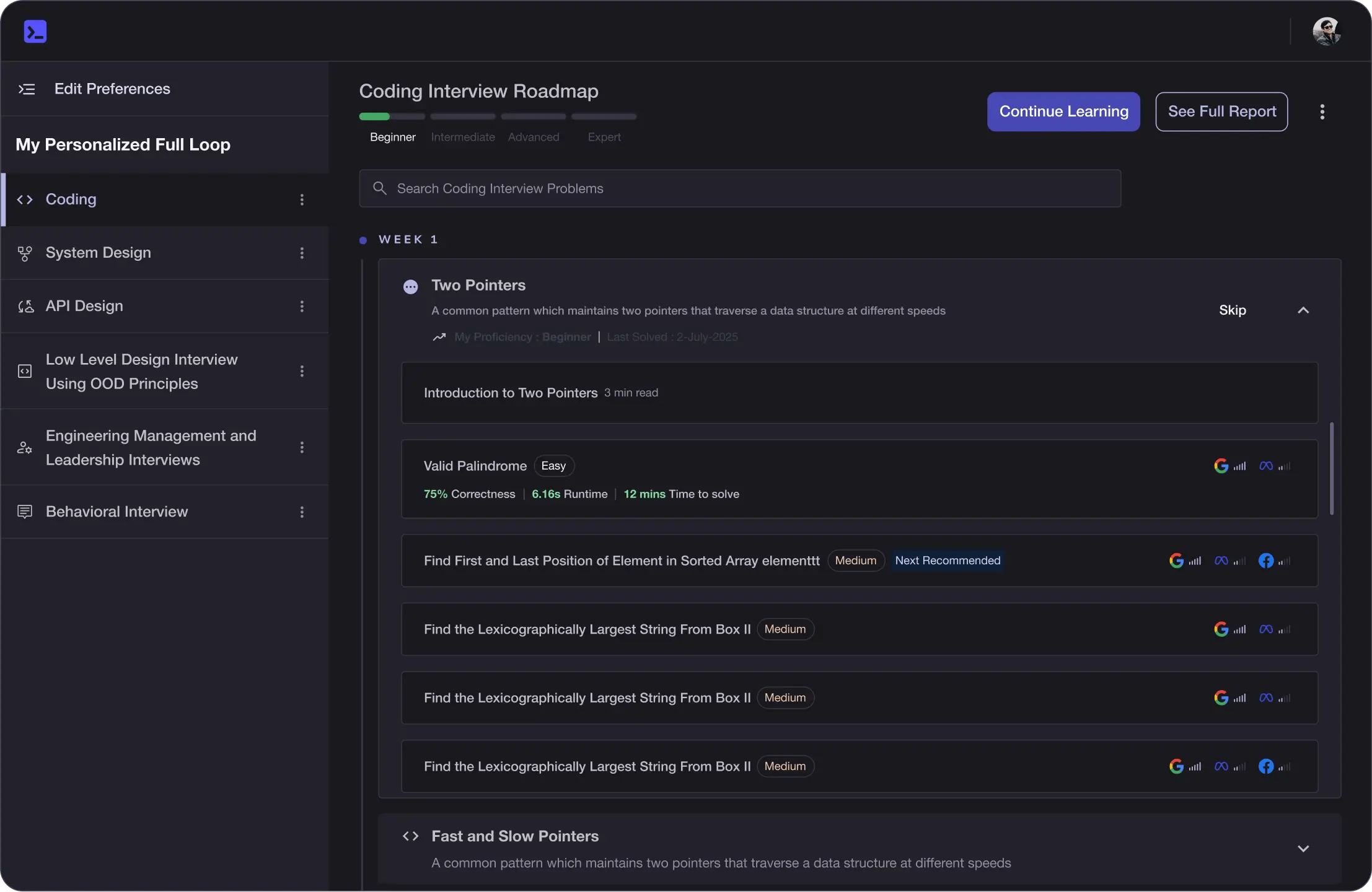
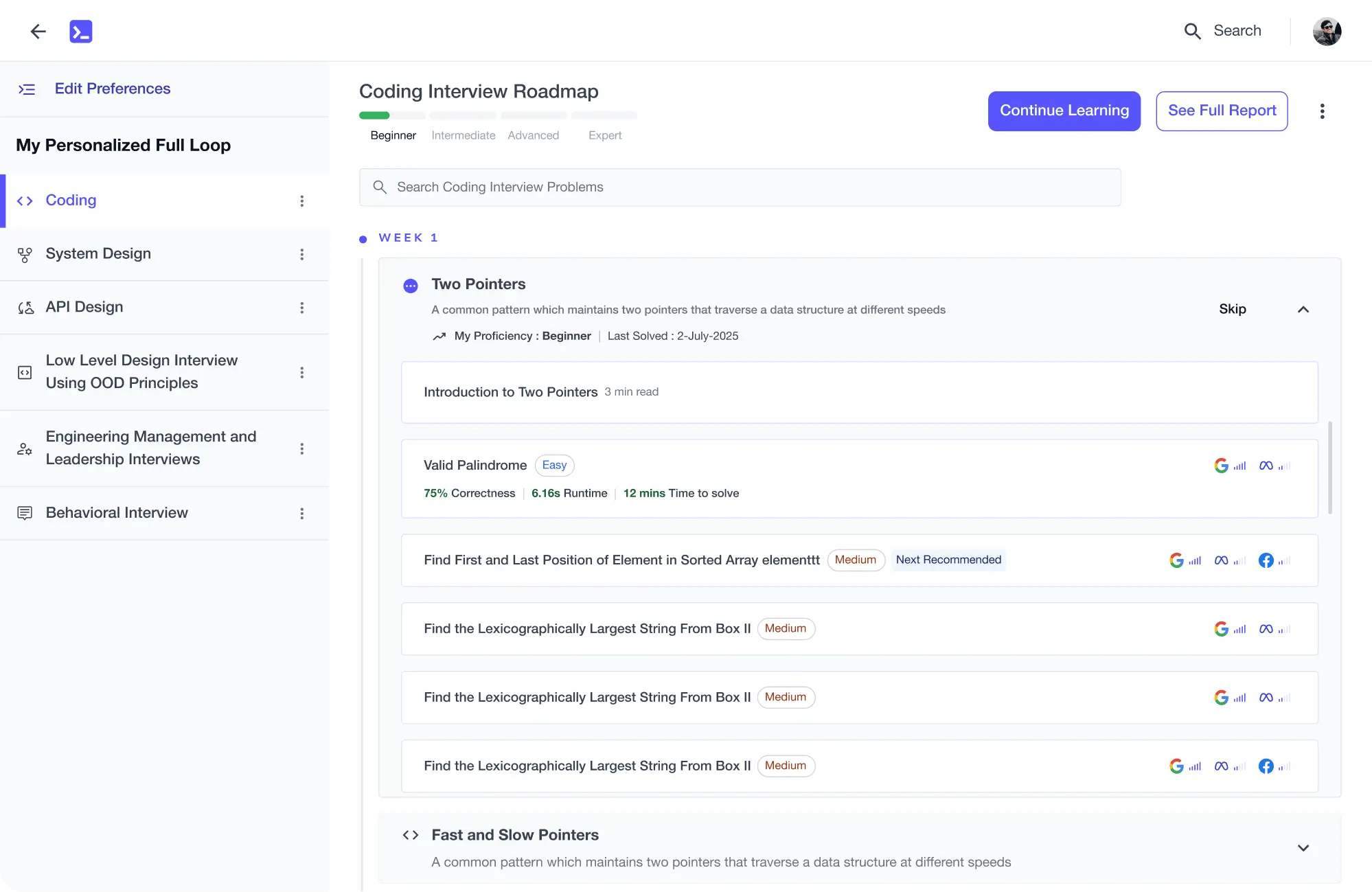
Personalized Roadmaps
The platform adapts to your strengths & skills gaps as you go
Future-proof Your Career
Get hands-on with in-demand skills
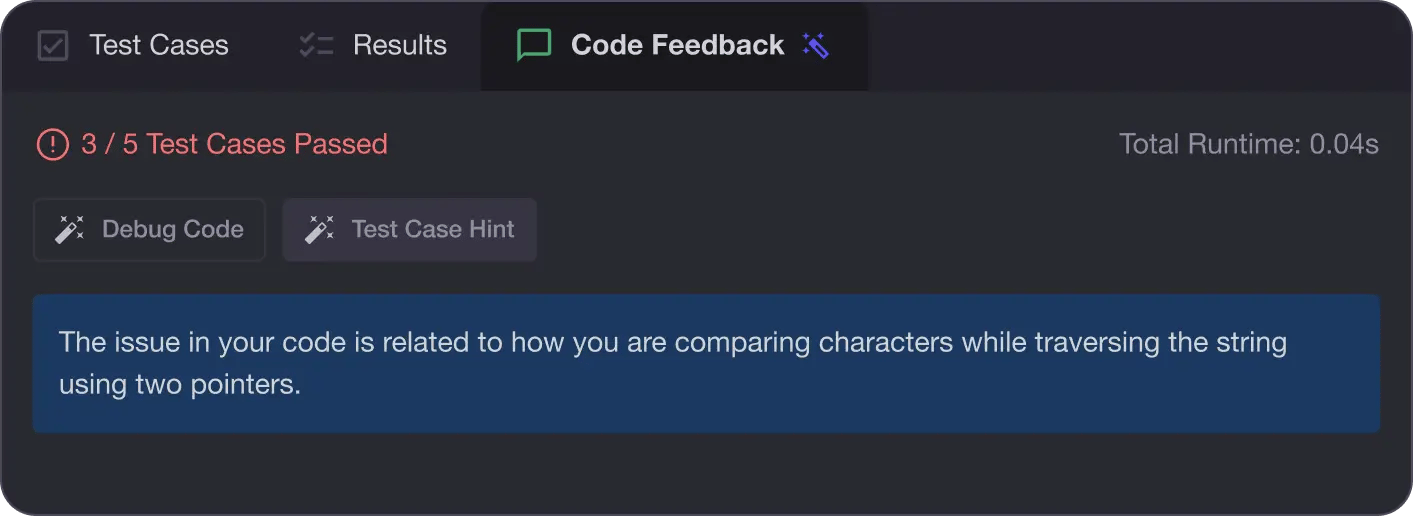
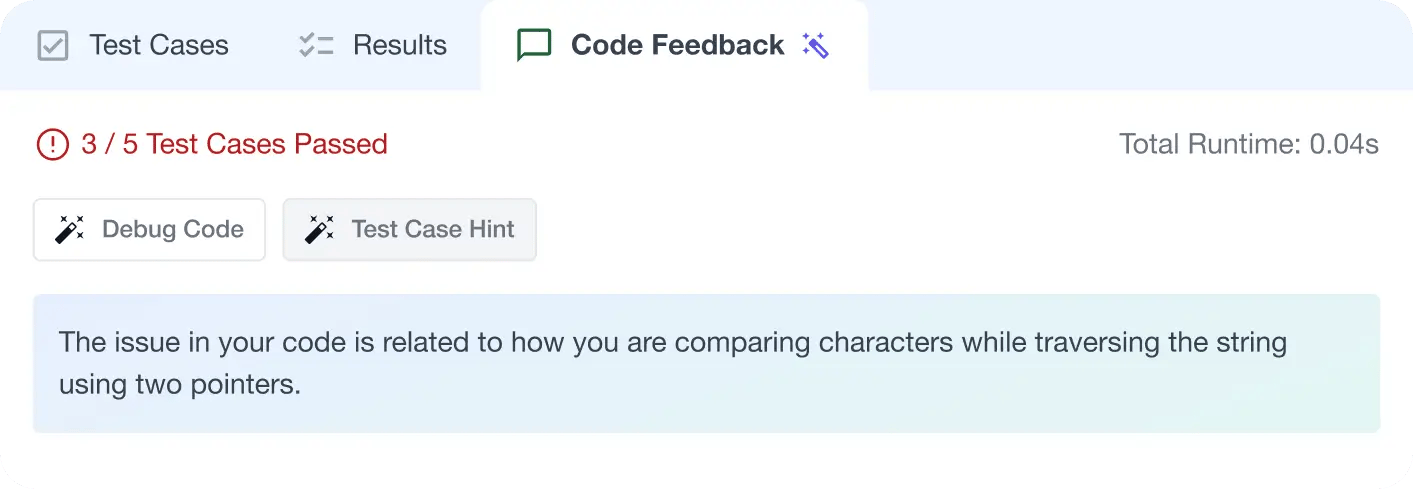
AI Code Mentor
Write better code with AI feedback, smart debugging, and "Ask AI"
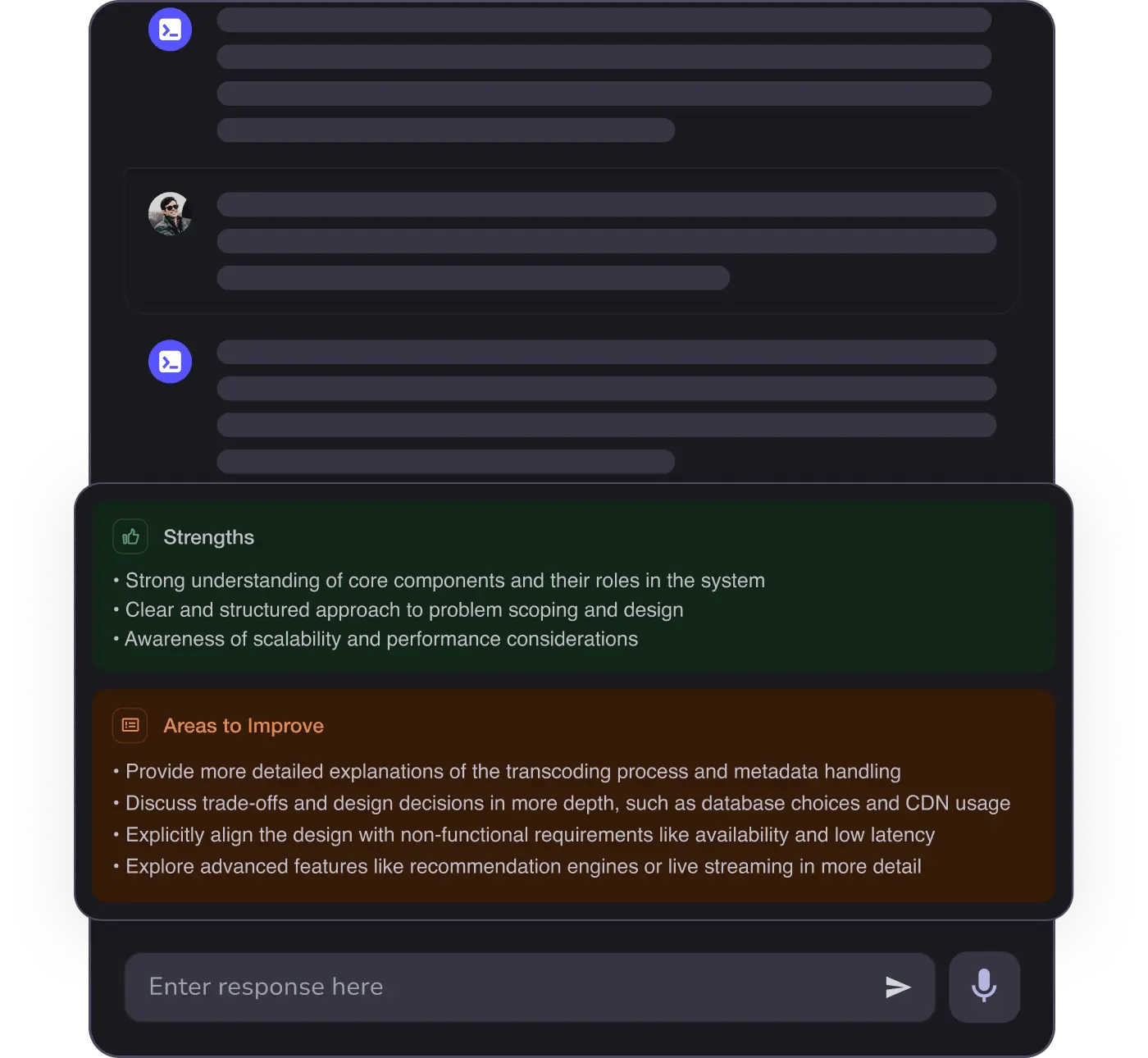
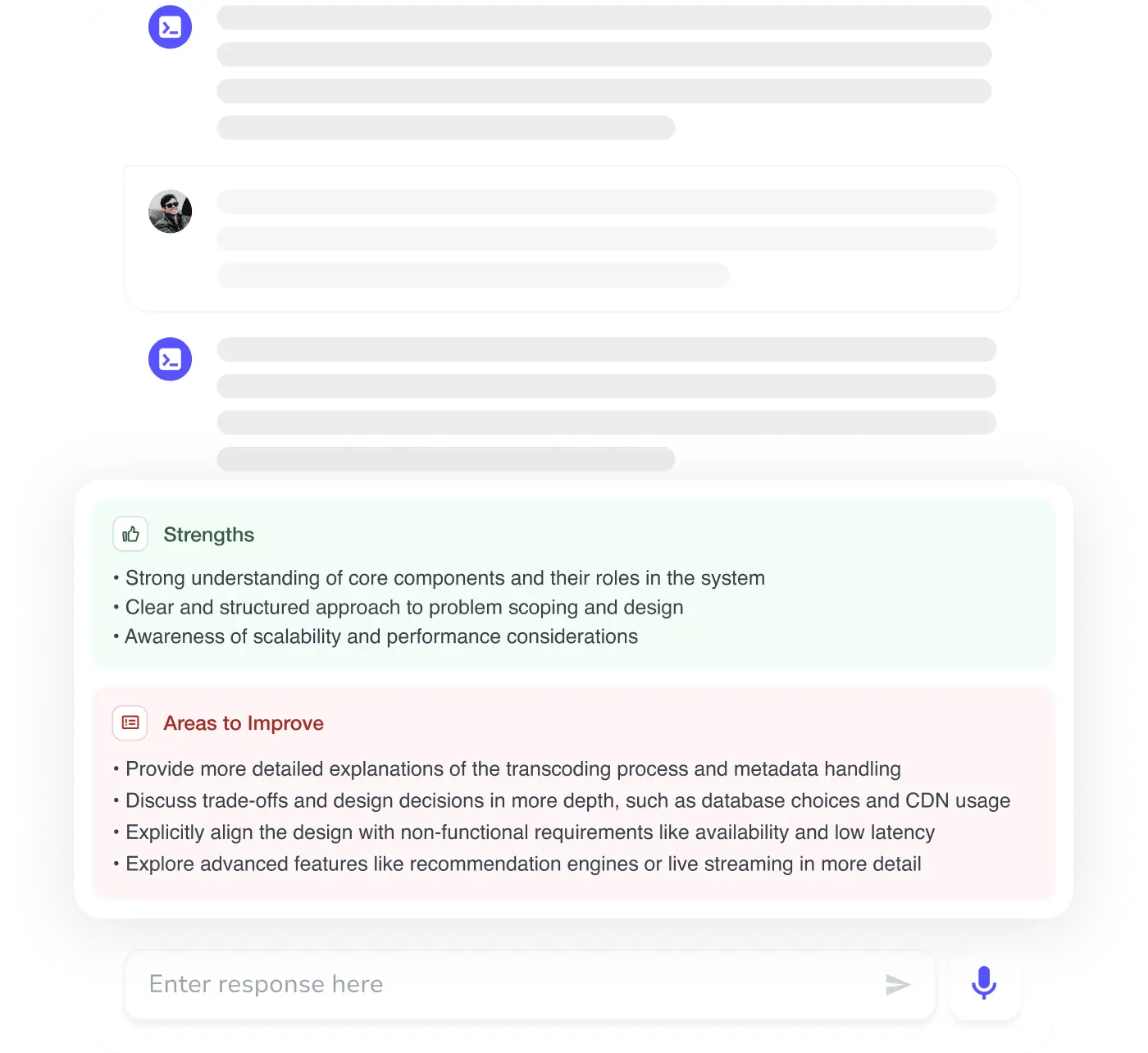
MAANG+ Interview Prep
AI Mock Interviews simulate every technical loop at top companies
Free Resources