Join 2.9 million developers at
Join 2.9 million developers at
LEARNING OBJECTIVES
- Basic understanding of how images and containers work
- Proficiency in Docker for building and managing containers
- Hands-on experience containerizing applications for easy deployment
- Understanding of microservices architecture basics
- Knowledge of Docker’s role in DevOps
Learning Roadmap
1.
About the Course
About the Course
Get familiar with Docker’s role in cloud tech and gain practical course insights.
2.
An Overview of Containers
An Overview of Containers
Explore the evolution from VMs to containers, emphasizing efficiency, portability, and cloud-native advancements.
3.
Docker and Container-Related Standards and Projects
Docker and Container-Related Standards and Projects
5 Lessons
5 Lessons
Examine Docker’s role, technology, key standards, and pivotal container projects.
4.
The Big Picture
The Big Picture
8 Lessons
8 Lessons
Explore Docker’s core concepts, from installation and image creation to container management and application deployment.
5.
The Docker Engine
The Docker Engine
6 Lessons
6 Lessons
Take a closer look at the modular components and architecture of the Docker Engine.
6.
Working with Images
Working with Images
15 Lessons
15 Lessons
Learn to manage Docker images, including creation, pulling, storage, tagging, security, and multi-architecture support.
7.
Working with Containers
Working with Containers
15 Lessons
15 Lessons
Master Docker containers by understanding their management, commands, debug tools, and life cycle practices.
8.
Containerizing an Application
Containerizing an Application
12 Lessons
12 Lessons
Sharpen your skills in containerizing applications using Docker, from writing Dockerfiles to multi-stage builds.
10.
Appendix: Getting Docker
Appendix: Getting Docker
5 Lessons
5 Lessons
Learn to install Docker on diverse platforms, including Windows, Mac, and Linux.
Certificate of Completion
Showcase your accomplishment by sharing your certificate of completion.
Complete more lessons to unlock your certificate
Show License and Attributions
Developed by MAANG Engineers
ABOUT THIS COURSE
Containers have revolutionized the IT world, making it difficult to know where to begin. This course will take you from basics to proficiency step by step.
You’ll start by learning the basics of containers and how they work. Then, you’ll explore key concepts like images and the Docker engine. With the basics out of the way, you’ll learn how to containerize and run an application. After completing this course, you’ll be ready to use Docker in the real world.
ABOUT THE AUTHOR
Nigel Poulton
Nigel is a Kubernetes and Docker Video Trainer extraordinaire, a popular Author and highly sought-after Public Speaker at tech conferences around the world.
Trusted by 2.9 million developers working at companies
A
Anthony Walker
@_webarchitect_
E
Evan Dunbar
ML Engineer
S
Software Developer
Carlos Matias La Borde
S
Souvik Kundu
Front-end Developer
V
Vinay Krishnaiah
Software Developer
Built for 10x Developers
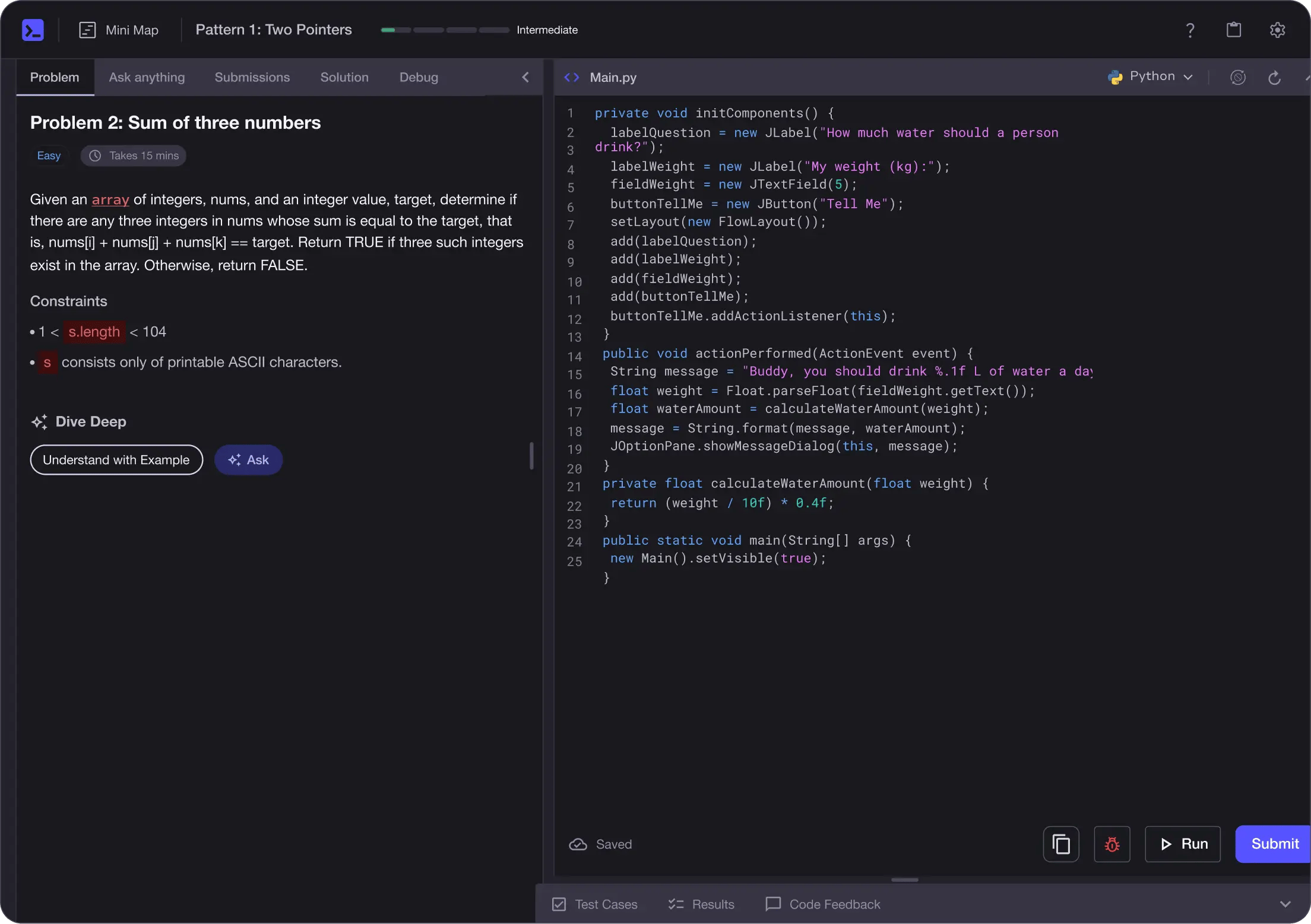
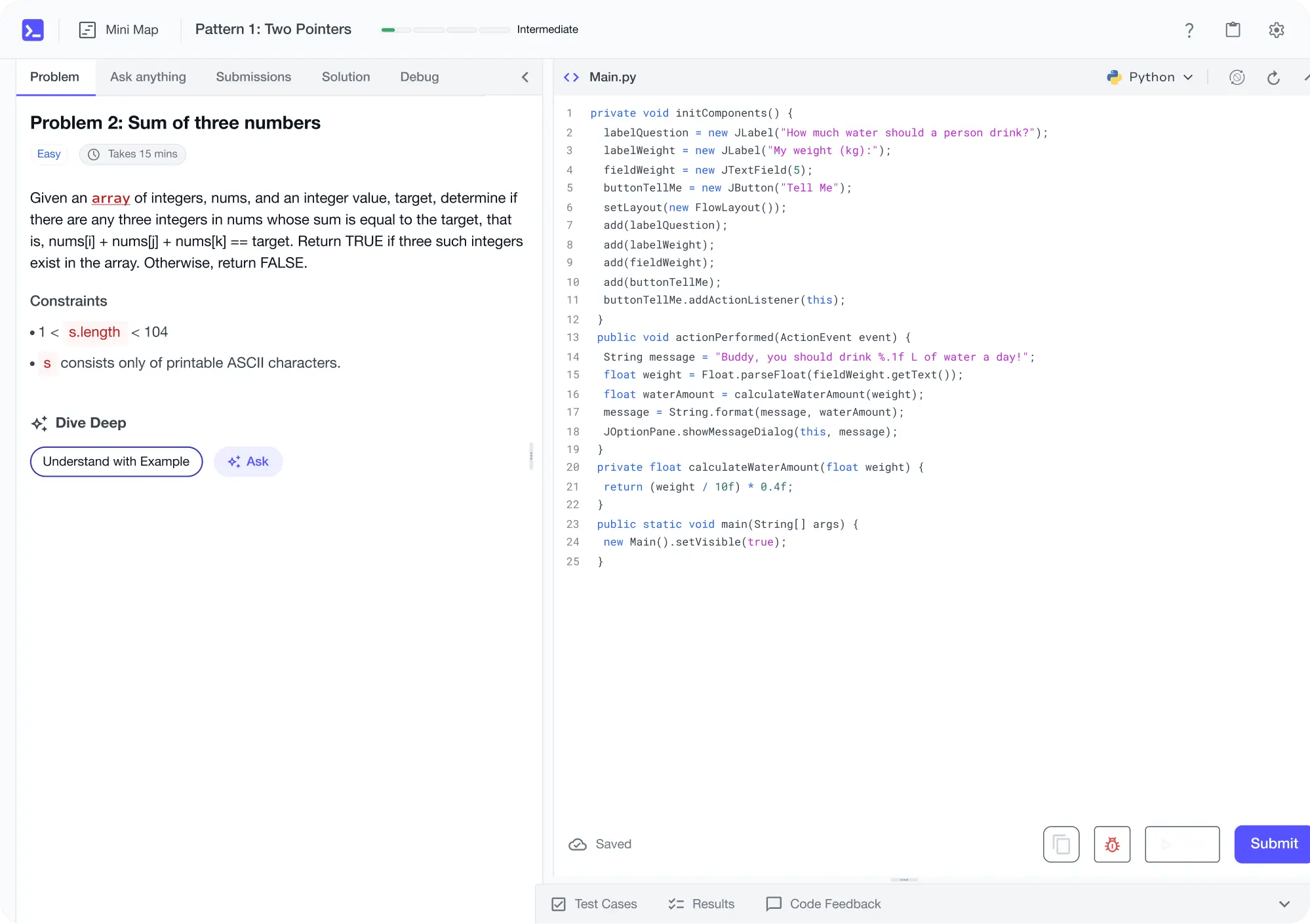
No Passive Learning
Learn by building with project-based lessons and in-browser code editor
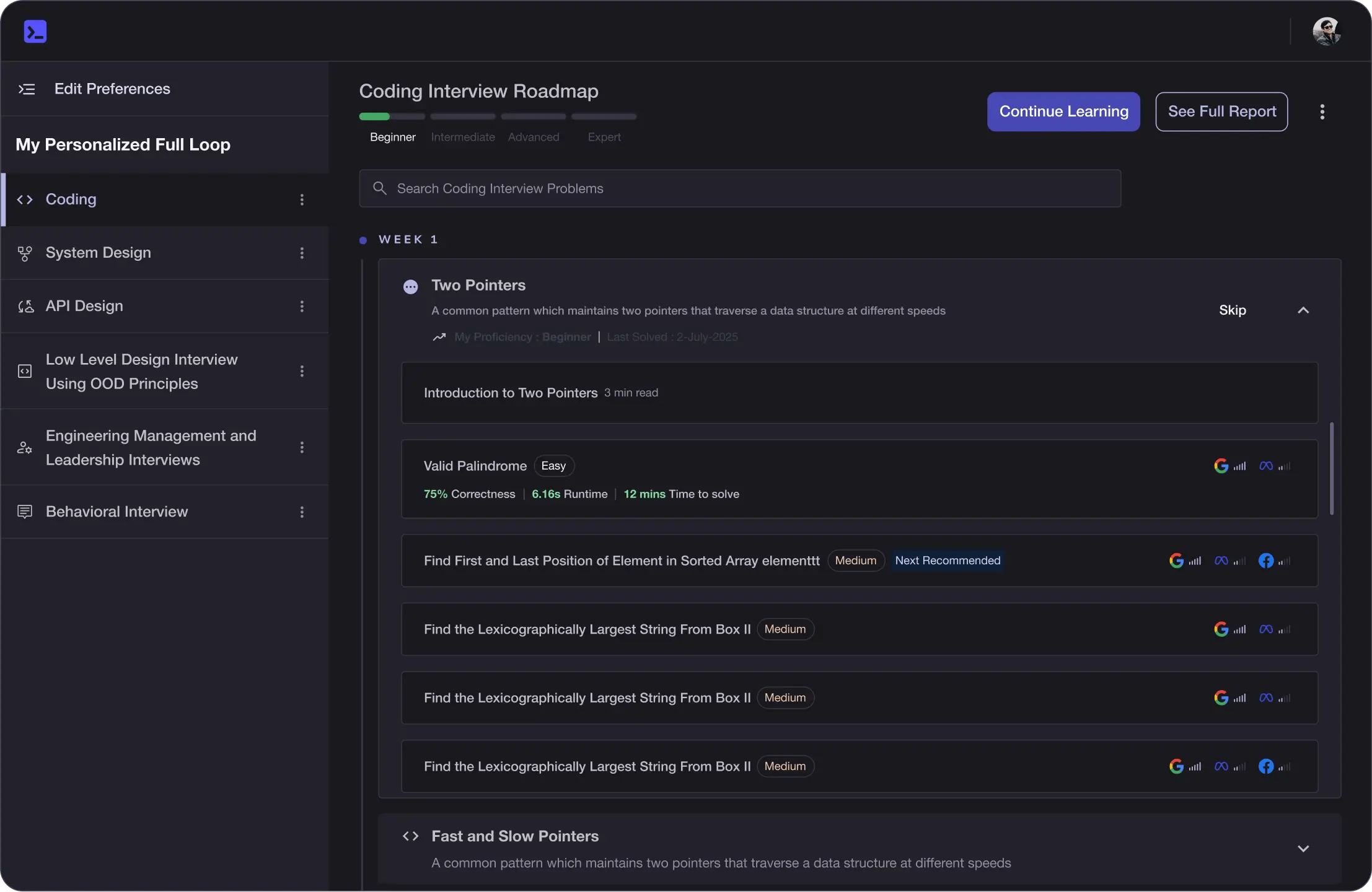
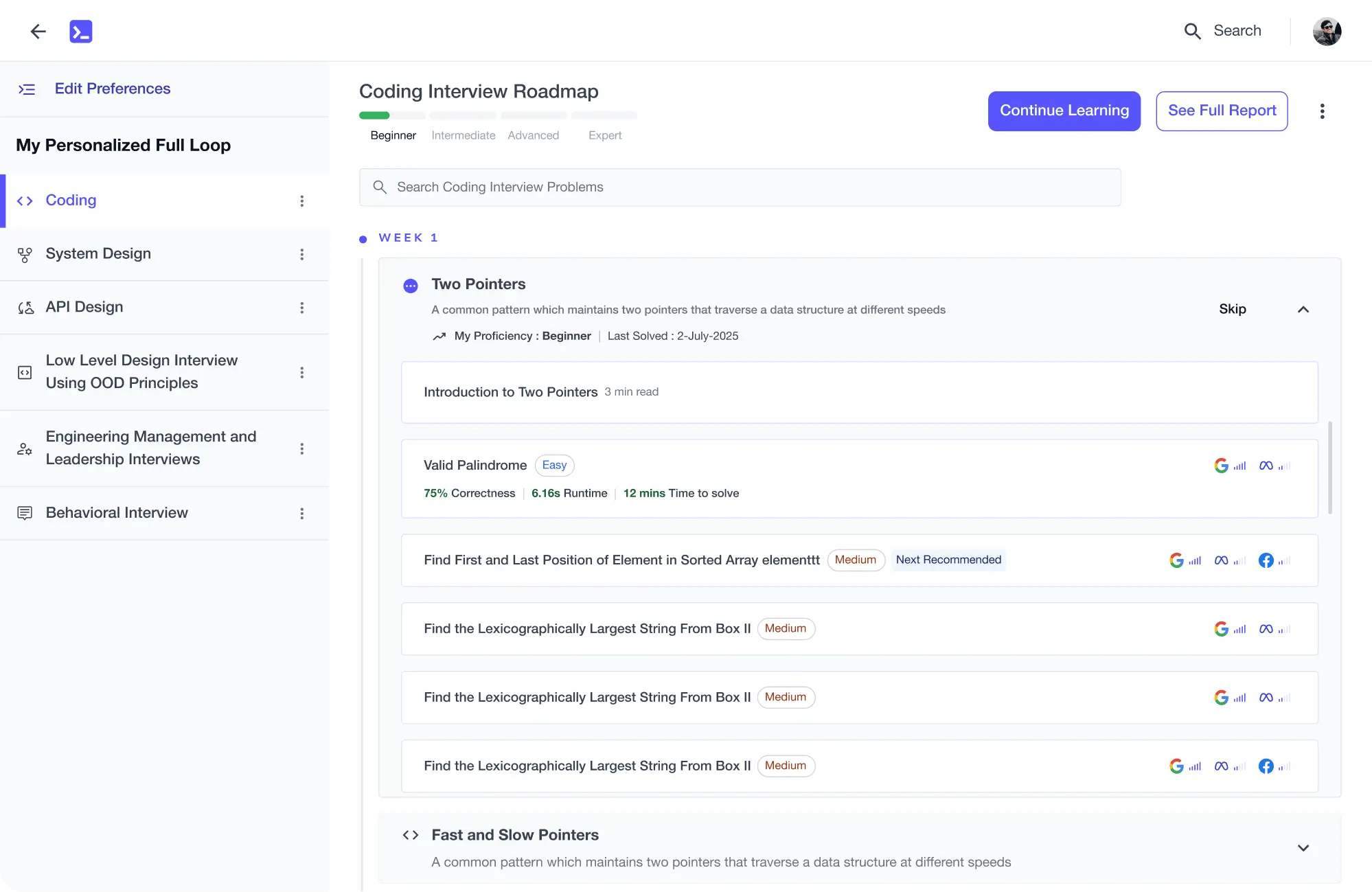
Personalized Roadmaps
The platform adapts to your strengths & skills gaps as you go
Future-proof Your Career
Get hands-on with in-demand skills
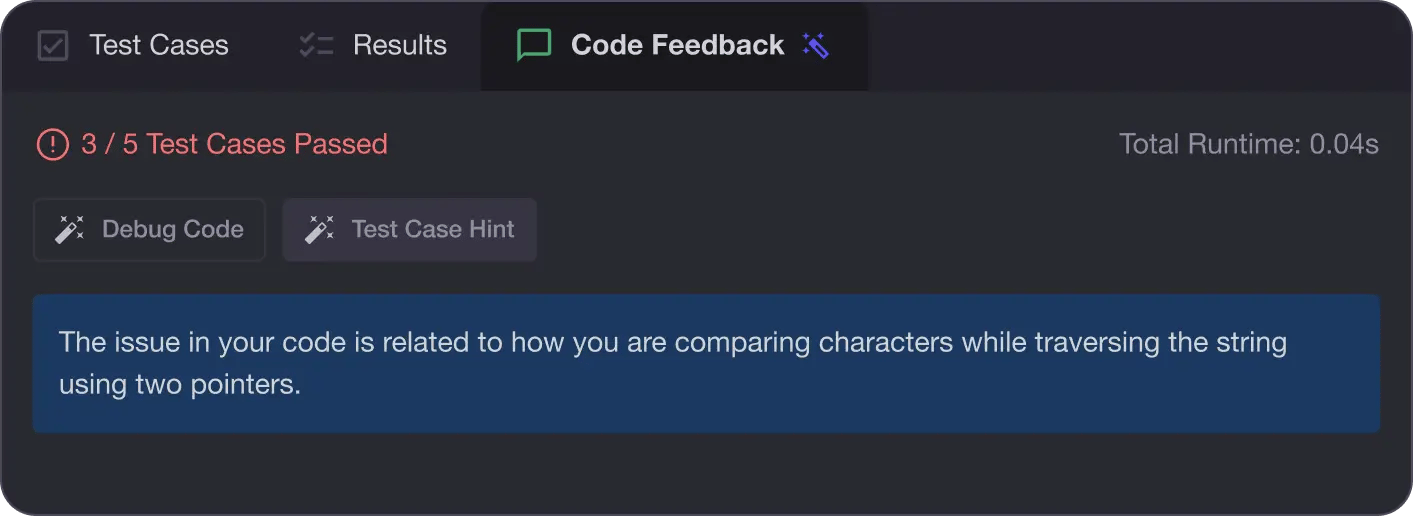
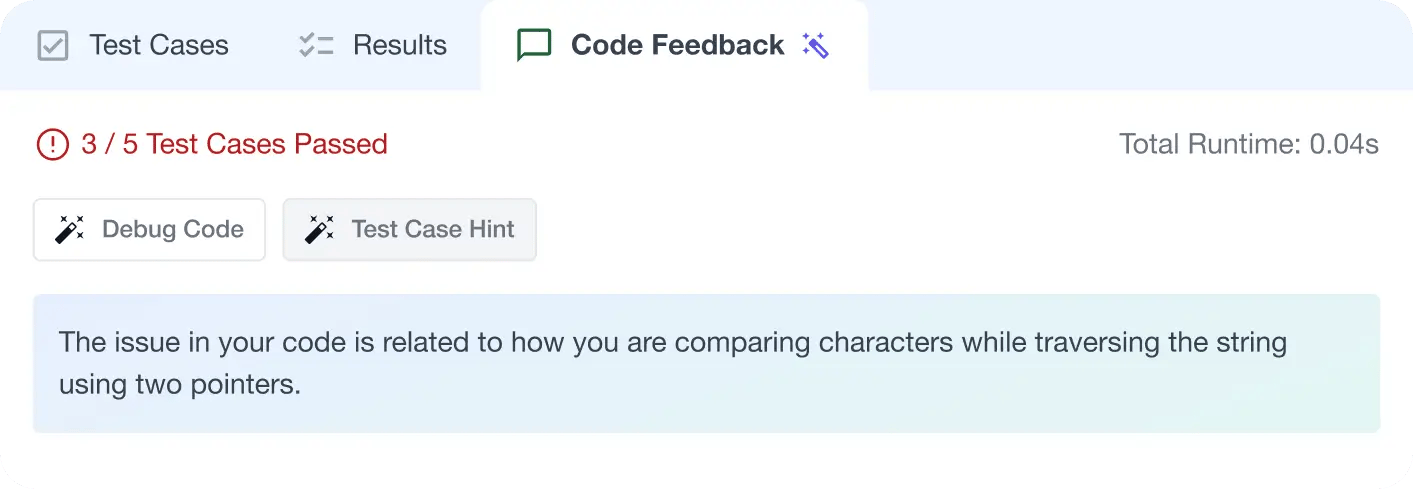
AI Code Mentor
Write better code with AI feedback, smart debugging, and "Ask AI"
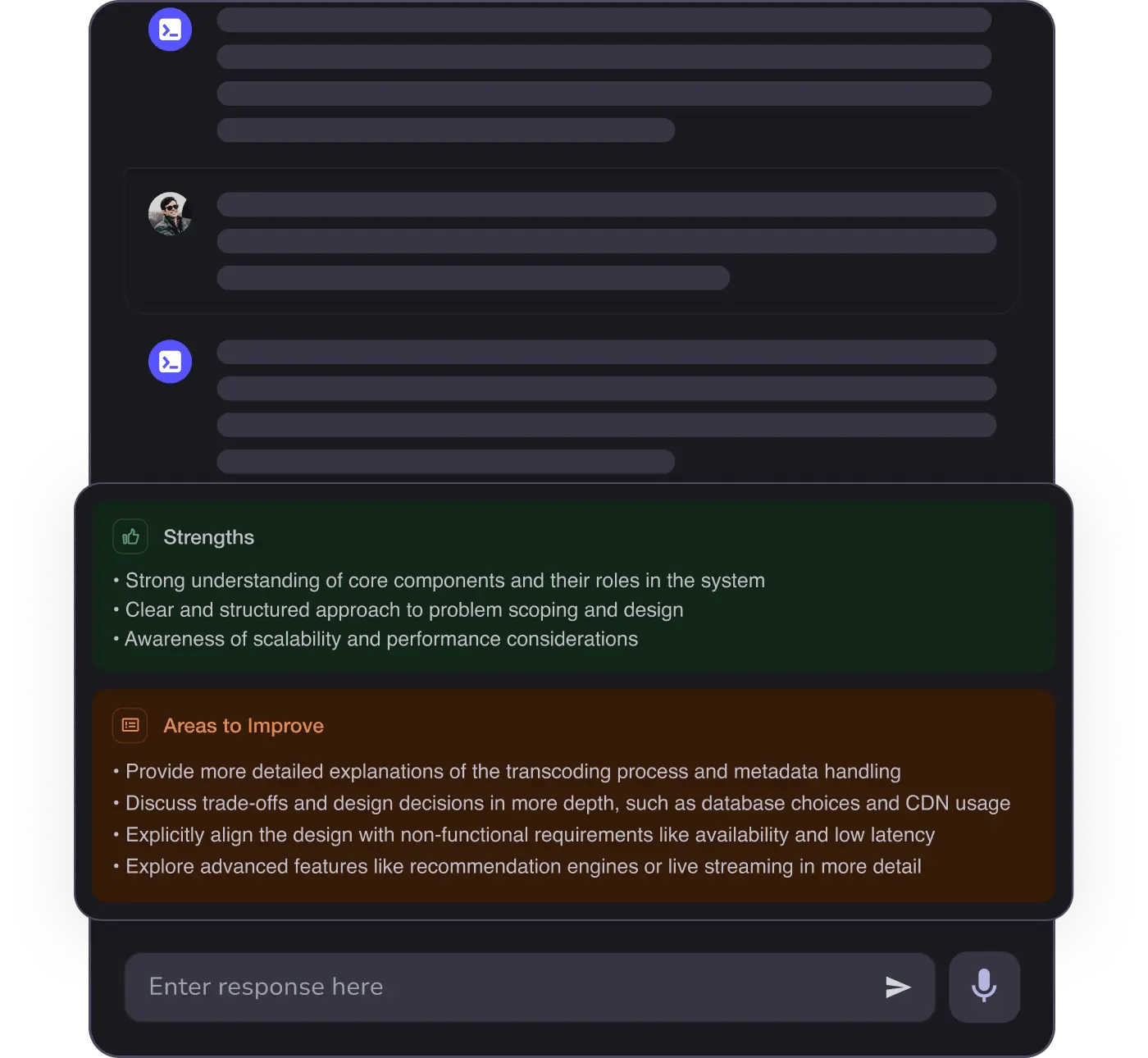
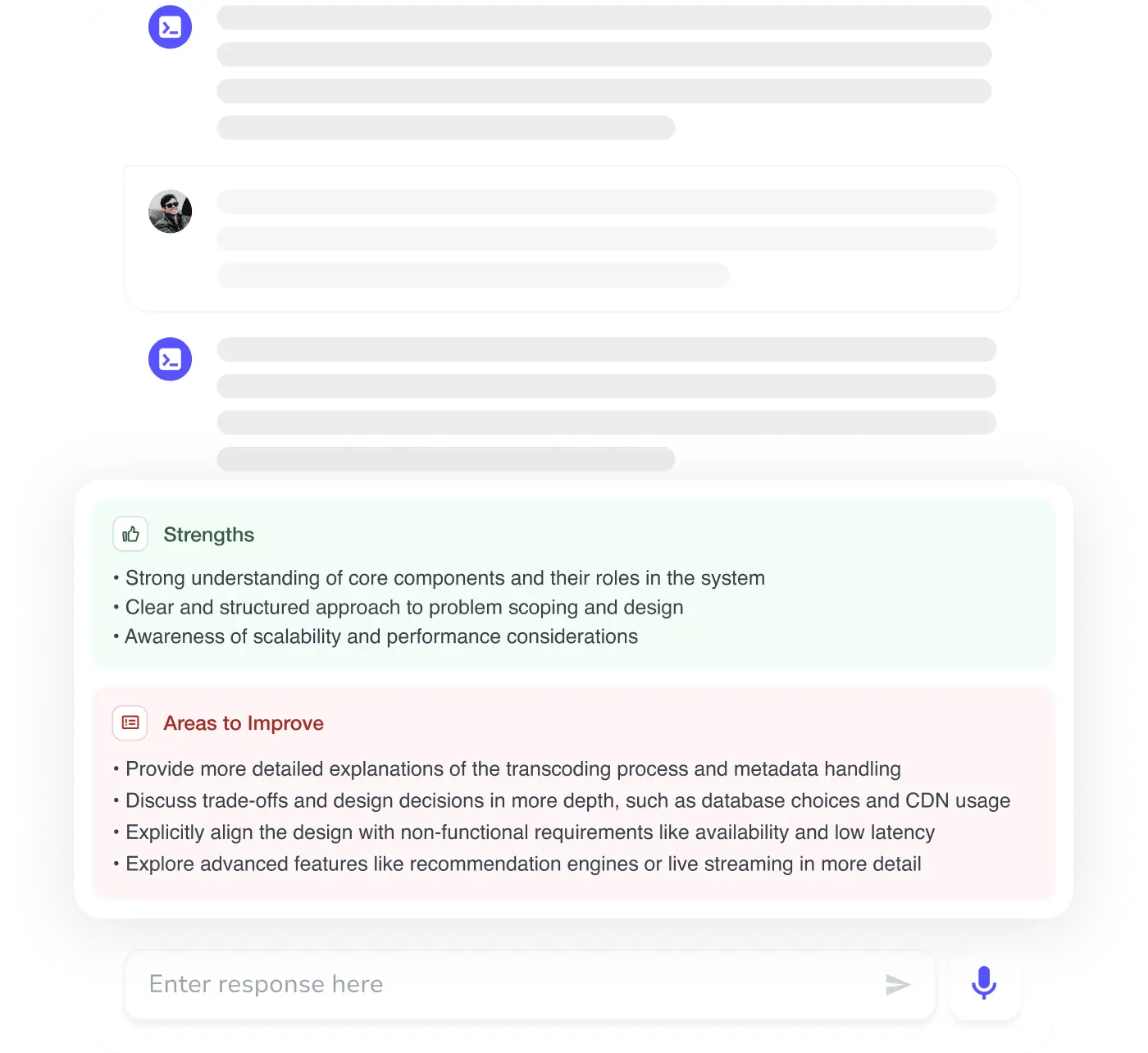
MAANG+ Interview Prep
AI Mock Interviews simulate every technical loop at top companies
Free Resources